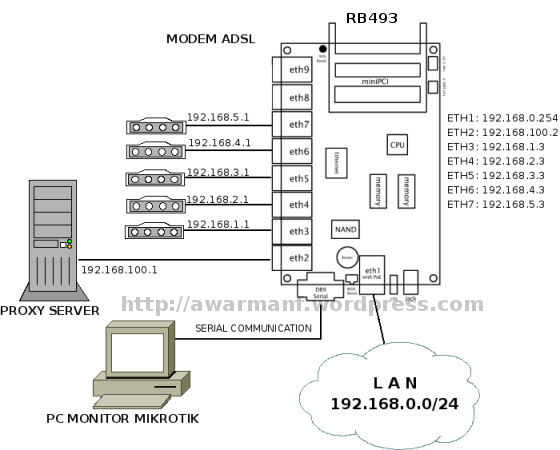
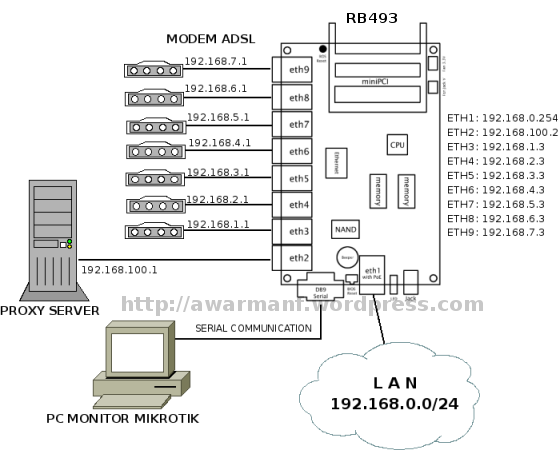
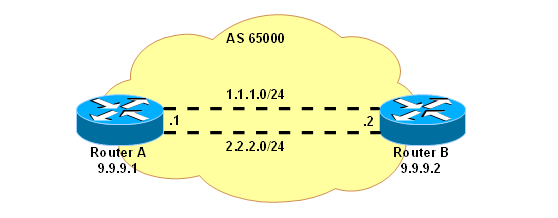
Menggunakan router board mikrotik RB493 dengan 5 interface WAN untuk
koneksi ke internet menggunakan speedy. Semua modem speedy diset router.
Pemodelan koneksi adalah sbb:
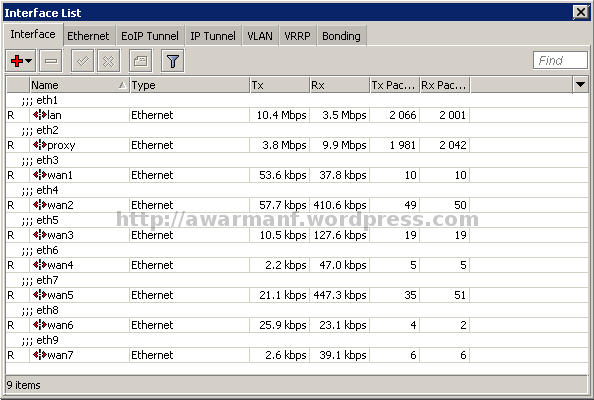
/interface ethernet
/ip adress
/ip adress
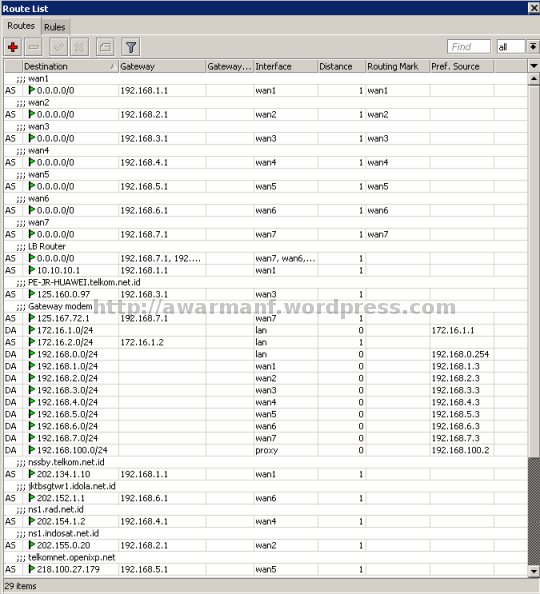
/ip route
Penjelasan:
/ip dns
/ip dns static
/system clock
/system ntp client
/system ntp server
/ip firewall filter
/ip firewall address-list
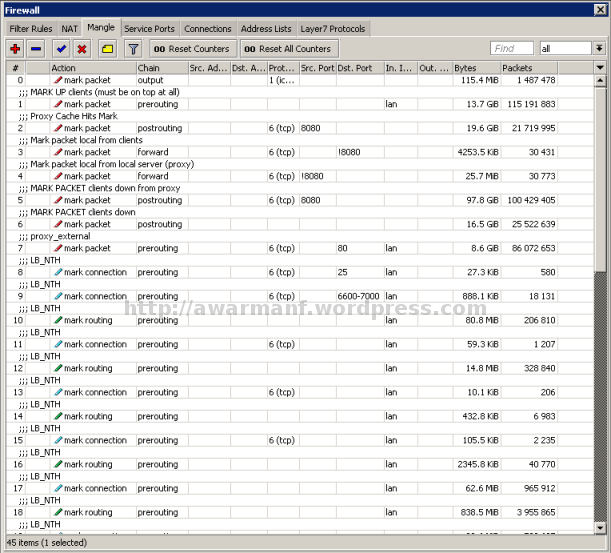
/ip firewall nat
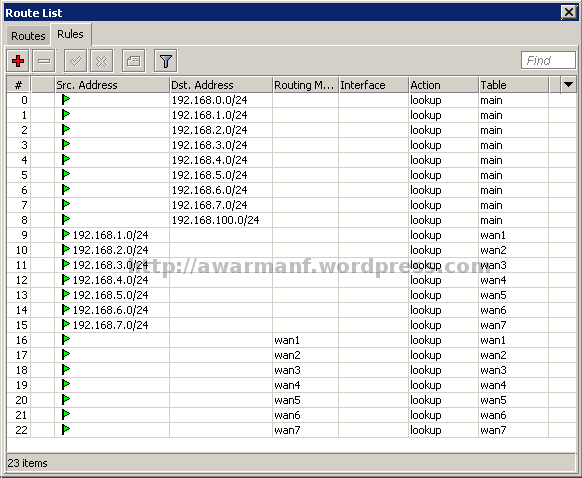
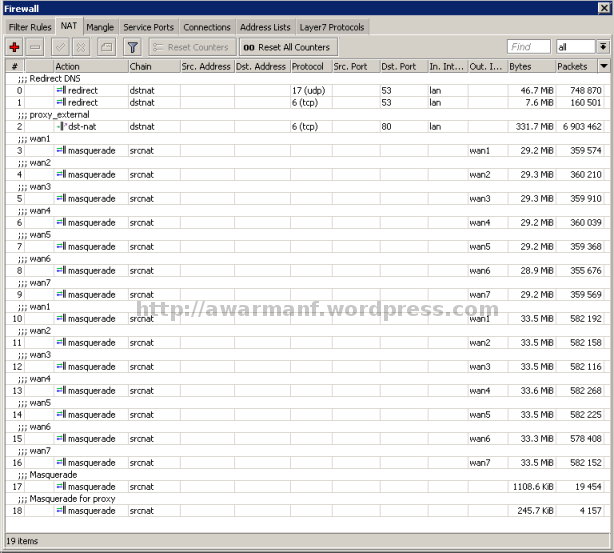
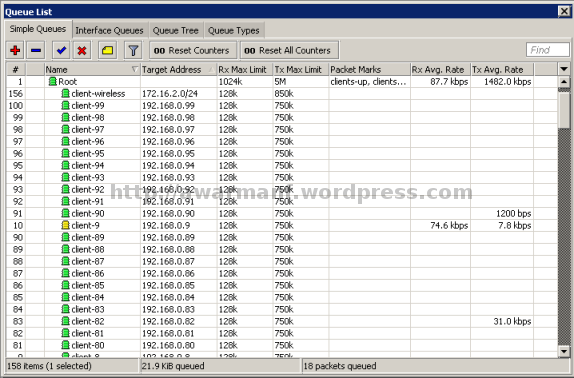
/ip firewall mangle
Baris-baris rule mangle yang berwarna hijau itu ditulis secara otomatis melalui script yang akan dijelaskan nanti.
param
Saat router reboot script param di bawah ini akan dieksekusi:
deadgwdetection
Script ini dijalankan via schedule setiap 120 detik atau 2 menit
Sekarang aktifkan schedule untuk dua script di atas:
/system scheduler
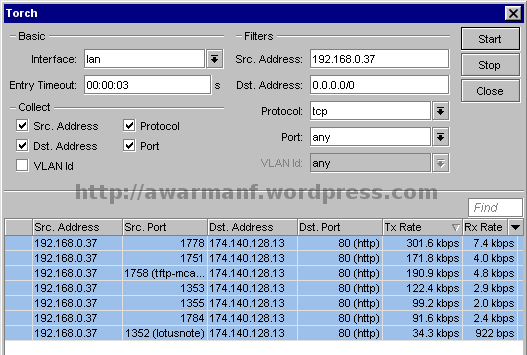
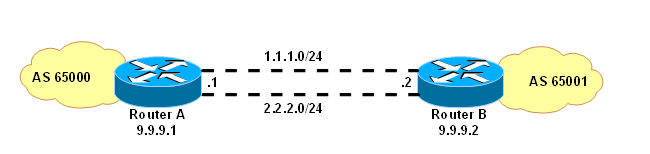
- Load Balancing menggunakan NTH untuk trafik browsing (tcp port 80) dan PCC untuk trafik non browsing.
- Koneksi ke speedy dianggap tidak stabil dan perlu dibuat fail over sehingga jika salah satu speedy putus maka Load Balancing PCC dan NTH masih berjalan.
- Koneksi internet user (clients) ke tcp port 80 (browsing) akan dilewatkan server proxy.
- Koneksi internet server proxy akan melalui Load Balancing NTH.
- Koneksi internet user (clients) selain browsing di atas akan melalui Load Balancing PCC.
/interface ethernet
set 0 arp=enabled auto-negotiation=yes comment=eth1 disabled=no full-duplex=\
yes l2mtu=1526 mac-address=00:XX:XX:XX:XX:8F mtu=1500 name=lan speed=\
100Mbps
set 1 arp=enabled auto-negotiation=yes bandwidth=unlimited/unlimited comment=\
eth2 disabled=no full-duplex=yes l2mtu=1522 mac-address=00:XX:XX:XX:XX:90 \
master-port=none mtu=1500 name=proxy speed=100Mbps
set 2 arp=enabled auto-negotiation=yes bandwidth=unlimited/unlimited comment=\
eth3 disabled=no full-duplex=yes l2mtu=1522 mac-address=00:XX:XX:XX:XX:91 \
master-port=none mtu=1500 name=wan1 speed=100Mbps
set 3 arp=enabled auto-negotiation=yes bandwidth=unlimited/unlimited comment=\
eth4 disabled=no full-duplex=yes l2mtu=1522 mac-address=00:XX:XX:XX:XX:92 \
master-port=none mtu=1500 name=wan2 speed=100Mbps
set 4 arp=enabled auto-negotiation=yes bandwidth=unlimited/unlimited comment=\
eth5 disabled=no full-duplex=yes l2mtu=1522 mac-address=00:XX:XX:XX:XX:93 \
master-port=none mtu=1500 name=wan3 speed=100Mbps
set 5 arp=enabled auto-negotiation=yes bandwidth=unlimited/unlimited comment=\
eth6 disabled=no full-duplex=yes l2mtu=1522 mac-address=00:XX:XX:XX:XX:94 \
master-port=none mtu=1500 name=wan4 speed=100Mbps
set 6 arp=enabled auto-negotiation=yes bandwidth=unlimited/unlimited comment=\
eth7 disabled=no full-duplex=yes l2mtu=1522 mac-address=00:XX:XX:XX:XX:95 \
master-port=none mtu=1500 name=wan5 speed=100Mbps
set 7 arp=enabled auto-negotiation=yes bandwidth=unlimited/unlimited comment=\
eth8 disabled=no full-duplex=yes l2mtu=1522 mac-address=00:XX:XX:XX:XX:95 \
master-port=none mtu=1500 name=ether8 speed=100Mbps
set 8 arp=enabled auto-negotiation=yes bandwidth=unlimited/unlimited comment=\
eth9 disabled=no full-duplex=yes l2mtu=1522 mac-address=00:XX:XX:XX:XX:97 \
master-port=none mtu=1500 name=ether9 speed=100Mbps
/ip adress
add address=192.168.0.254/24 broadcast=192.168.0.255 comment="" disabled=no \
interface=lan network=192.168.0.0
add address=192.168.100.2/24 broadcast=192.168.100.255 comment="" disabled=no \
interface=proxy network=192.168.100.0
add address=192.168.1.3/24 broadcast=192.168.1.255 comment="" disabled=no \
interface=wan1 network=192.168.1.0
add address=192.168.2.3/24 broadcast=192.168.2.255 comment="" disabled=no \
interface=wan2 network=192.168.2.0
add address=192.168.3.3/24 broadcast=192.168.3.255 comment="" disabled=no \
interface=wan3 network=192.168.3.0
add address=192.168.4.3/24 broadcast=192.168.4.255 comment="" disabled=no \
interface=wan4 network=192.168.4.0
add address=192.168.5.3/24 broadcast=192.168.5.255 comment="" disabled=no \
interface=wan5 network=192.168.5.0
/ip adress
add address=192.168.0.254/24 broadcast=192.168.0.255 comment="" disabled=no \
interface=lan network=192.168.0.0
add address=192.168.100.2/24 broadcast=192.168.100.255 comment="" disabled=no \
interface=proxy network=192.168.100.0
add address=192.168.1.3/24 broadcast=192.168.1.255 comment="" disabled=no \
interface=wan1 network=192.168.1.0
add address=192.168.2.3/24 broadcast=192.168.2.255 comment="" disabled=no \
interface=wan2 network=192.168.2.0
add address=192.168.3.3/24 broadcast=192.168.3.255 comment="" disabled=no \
interface=wan3 network=192.168.3.0
add address=192.168.4.3/24 broadcast=192.168.4.255 comment="" disabled=no \
interface=wan4 network=192.168.4.0
add address=192.168.5.3/24 broadcast=192.168.5.255 comment="" disabled=no \
interface=wan5 network=192.168.5.0
/ip route
add comment=wan1 disabled=no distance=1 dst-address=0.0.0.0/0 gateway=\
192.168.1.1 routing-mark=wan1 scope=255 target-scope=10
add comment=wan2 disabled=no distance=1 dst-address=0.0.0.0/0 gateway=\
192.168.2.1 routing-mark=wan2 scope=255 target-scope=10
add comment=wan3 disabled=no distance=1 dst-address=0.0.0.0/0 gateway=\
192.168.3.1 routing-mark=wan3 scope=255 target-scope=10
add comment=wan4 disabled=no distance=1 dst-address=0.0.0.0/0 gateway=\
192.168.4.1 routing-mark=wan4 scope=255 target-scope=10
add comment=wan5 disabled=no distance=1 dst-address=0.0.0.0/0 gateway=\
192.168.5.1 routing-mark=wan5 scope=255 target-scope=10
add comment=nssby.telkom.net.id disabled=no distance=1 dst-address=\
202.134.1.10/32 gateway=192.168.1.1 scope=30 target-scope=10
add comment=ns1.indosat.net.id disabled=no distance=1 dst-address=\
202.155.0.20/32 gateway=192.168.2.1 scope=30 target-scope=10
add comment=PE-JR-HUAWEI.telkom.net.id disabled=no distance=1 dst-address=\
125.160.0.97/32 gateway=192.168.3.1 scope=30 target-scope=10
add comment=ns1.rad.net.id disabled=no distance=1 dst-address=202.154.1.2/32 \
gateway=192.168.4.1 scope=30 target-scope=10
add comment=ns1.indosat.net.id disabled=no distance=1 dst-address=\
202.155.0.15/32 gateway=192.168.5.1 scope=30 target-scope=10
add check-gateway=ping comment="LB Router" disabled=no distance=1 \
dst-address=0.0.0.0/0 \
gateway=192.168.5.1,192.168.4.1,192.168.3.1,192.168.2.1,192.168.1.1
scope=255 target-scope=10
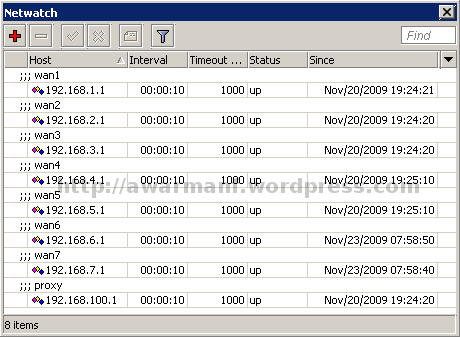
Penjelasan:
- Baris routing yang berwarna hijau ditulis secara otomatis oleh script.
- Koneksi dari router keluar (internet) akan melalui semua gateway yang hidup (dalam contoh di atas ada 5 gateway).
- Untuk deteksi koneksi internet masing-masing wan dilakukan dengan cara ping ke ip tertentu di mana routing ke ip tersebut sudah dibuat statik per wan.
- Untuk cek koneksi wan1 dilakukan dengan ping ke ip 202.134.1.10
- Untuk cek koneksi wan2 dilakukan dengan ping ke ip 202.155.0.20
- Untuk cek koneksi wan3 dilakukan dengan ping ke ip 125.160.0.97
- Untuk cek koneksi wan4 dilakukan dengan ping ke ip 202.154.1.2
- Untuk cek koneksi wan5 dilakukan dengan ping ke ip 202.154.0.15
/ip dns
set allow-remote-requests=yes cache-max-ttl=1w cache-size=3072KiB \
max-udp-packet-size=512 primary-dns=202.134.0.155 secondary-dns=\
203.130.196.155
/ip dns static
add address=192.168.0.254 disabled=no name=cache-ns.domainku.org ttl=1d
/system clock
set time-zone-name=Asia/Jakarta
/system ntp client
set enabled=yes mode=unicast primary-ntp=202.162.32.12 secondary-ntp=203.160.128.3
/system ntp server
set broadcast=no enabled=yes manycast=yes multicast=no
/ip firewall filter
add action=add-src-to-address-list address-list="port scanners" \
address-list-timeout=2w chain=input comment="Port scanners to list " \
disabled=no in-interface=wan1 protocol=tcp psd=21,3s,3,1
add action=add-src-to-address-list address-list="port scanners" \
address-list-timeout=2w chain=input comment="Port scanners to list " \
disabled=no in-interface=wan2 protocol=tcp psd=21,3s,3,1
add action=add-src-to-address-list address-list="port scanners" \
address-list-timeout=2w chain=input comment="Port scanners to list " \
disabled=no in-interface=wan3 protocol=tcp psd=21,3s,3,1
add action=add-src-to-address-list address-list="port scanners" \
address-list-timeout=2w chain=input comment="Port scanners to list " \
disabled=no in-interface=wan4 protocol=tcp psd=21,3s,3,1
add action=add-src-to-address-list address-list="port scanners" \
address-list-timeout=2w chain=input comment="Port scanners to list " \
disabled=no in-interface=wan5 protocol=tcp psd=21,3s,3,1
add action=add-src-to-address-list address-list="port scanners" \
address-list-timeout=2w chain=input comment="Port scanners to list " \
disabled=no in-interface=proxy protocol=tcp psd=21,3s,3,1
add action=add-src-to-address-list address-list="port scanners" \
address-list-timeout=2w chain=input comment="NMAP FIN Stealth scan" \
disabled=no protocol=tcp tcp-flags=fin,!syn,!rst,!psh,!ack,!urg
add action=add-src-to-address-list address-list="port scanners" \
address-list-timeout=2w chain=input comment="SYN/FIN scan" disabled=no \
protocol=tcp tcp-flags=fin,syn
add action=add-src-to-address-list address-list="port scanners" \
address-list-timeout=2w chain=input comment="SYN/RST scan" disabled=no \
protocol=tcp tcp-flags=syn,rst
add action=add-src-to-address-list address-list="port scanners" \
address-list-timeout=2w chain=input comment="FIN/PSH/URG scan" disabled=\
no protocol=tcp tcp-flags=fin,psh,urg,!syn,!rst,!ack
add action=add-src-to-address-list address-list="port scanners" \
address-list-timeout=2w chain=input comment="ALL/ALL scan" disabled=no \
protocol=tcp tcp-flags=fin,syn,rst,psh,ack,urg
add action=add-src-to-address-list address-list="port scanners" \
address-list-timeout=2w chain=input comment="NMAP NULL scan" disabled=no \
protocol=tcp tcp-flags=!fin,!syn,!rst,!psh,!ack,!urg
add action=drop chain=input comment="dropping port scanners" disabled=no \
src-address-list="port scanners"
add action=accept chain=input comment="Allow Established connections" \
connection-state=established disabled=no
add action=accept chain=input comment="Allow UDP" disabled=no protocol=udp
add action=accept chain=input comment="Allow limited pings" disabled=no \
limit=50/5s,2 protocol=icmp
add action=drop chain=input comment="Drop excess pings" disabled=no protocol=\
icmp
add action=drop chain=input comment="drop ssh brute forcers" disabled=no \
dst-port=22 in-interface=!proxy protocol=tcp src-address-list=\
ssh_blacklist
add action=add-src-to-address-list address-list=ssh_blacklist \
address-list-timeout=1w3d chain=input comment="" connection-state=new \
disabled=no dst-port=22 in-interface=!proxy protocol=tcp \
src-address-list=ssh_stage3
add action=add-src-to-address-list address-list=ssh_stage3 \
address-list-timeout=1m chain=input comment="" connection-state=new \
disabled=no dst-port=22 in-interface=!proxy protocol=tcp \
src-address-list=ssh_stage2
add action=add-src-to-address-list address-list=ssh_stage2 \
address-list-timeout=1m chain=input comment="" connection-state=new \
disabled=no dst-port=22 in-interface=!proxy protocol=tcp \
src-address-list=ssh_stage1
add action=add-src-to-address-list address-list=ssh_stage1 \
address-list-timeout=1m chain=input comment="" connection-state=new \
disabled=no dst-port=22 in-interface=!proxy protocol=tcp
add action=accept chain=input comment="SSH for secure shell" disabled=no \
dst-port=22 protocol=tcp
add action=drop chain=forward comment="drop ssh brute downstream" disabled=no \
dst-port=22 protocol=tcp src-address-list=ssh_blacklist
add action=accept chain=input comment=winbox disabled=no dst-port=8291 \
protocol=tcp
add action=accept chain=input comment="Allow input from clients" disabled=no \
src-address-list=clients
add action=drop chain=input comment="Drop Invalid connections" \
connection-state=invalid disabled=no
add action=drop chain=forward comment="drop invalid connections" \
connection-state=invalid disabled=no protocol=tcp
add action=accept chain=forward comment=\
"allow already established connections" connection-state=established \
disabled=no
add action=accept chain=forward comment="allow related connections" \
connection-state=related disabled=no
add action=accept chain=forward comment="Enable to exceptions" disabled=no \
dst-address-list=exceptions in-interface=lan src-address-list=clients
add action=drop chain=forward comment="" disabled=no src-address=0.0.0.0/8
add action=drop chain=forward comment="" disabled=no dst-address=0.0.0.0/8
add action=drop chain=forward comment="" disabled=no src-address=127.0.0.0/8
add action=drop chain=forward comment="" disabled=no dst-address=127.0.0.0/8
add action=drop chain=forward comment="" disabled=no src-address=224.0.0.0/3
add action=drop chain=forward comment="" disabled=no dst-address=224.0.0.0/3
add action=drop chain=forward comment="Drop to private networks" disabled=no \
dst-address-list=private-networks in-interface=lan
add action=jump chain=forward comment="" disabled=no jump-target=tcp \
protocol=tcp
add action=jump chain=forward comment="" disabled=no jump-target=udp \
protocol=udp
add action=jump chain=forward comment="" disabled=no jump-target=icmp \
protocol=icmp
add action=drop chain=forward comment="Port scanners to list " disabled=no \
protocol=tcp psd=21,3s,3,1
add action=drop chain=forward comment="NMAP FIN Stealth scan" disabled=no \
protocol=tcp tcp-flags=fin,!syn,!rst,!psh,!ack,!urg
add action=drop chain=forward comment="SYN/FIN scan" disabled=no protocol=tcp \
tcp-flags=fin,syn
add action=drop chain=forward comment="SYN/RST scan" disabled=no protocol=tcp \
tcp-flags=syn,rst
add action=drop chain=forward comment="FIN/PSH/URG scan" disabled=no \
protocol=tcp tcp-flags=fin,psh,urg,!syn,!rst,!ack
add action=drop chain=forward comment="ALL/ALL scan" disabled=no protocol=tcp \
tcp-flags=fin,syn,rst,psh,ack,urg
add action=drop chain=forward comment="NMAP NULL scan" disabled=no protocol=\
tcp tcp-flags=!fin,!syn,!rst,!psh,!ack,!urg
add action=drop chain=forward comment="dropping port scanners" disabled=no \
src-address-list="port scanners"
add action=accept chain=forward comment="Menghindari Spam SMTP Dari Virus" \
disabled=no dst-port=25 protocol=tcp src-address-list=smtp-email
add action=add-src-to-address-list address-list=smtp-email \
address-list-timeout=5m chain=forward comment="" disabled=no dst-port=25 \
protocol=tcp
add action=drop chain=forward comment="" disabled=no dst-port=25 protocol=tcp
add action=drop chain=forward comment="Drop tcp syn from client > 20" \
connection-limit=30,32 disabled=no in-interface=lan protocol=tcp \
tcp-flags=syn
add action=accept chain=forward comment="Allow forward from clients" \
disabled=no in-interface=lan src-address-list=clients
add action=accept chain=forward comment="Allow from proxy" disabled=no \
src-address-list=proxy
add action=drop chain=forward comment="Drop connection from lan" disabled=no \
in-interface=lan
add action=drop chain=tcp comment="deny TFTP" disabled=no dst-port=69 \
protocol=tcp
add action=drop chain=tcp comment="deny RPC portmapper" disabled=no dst-port=\
111 protocol=tcp
add action=drop chain=tcp comment="deny NFS" disabled=no dst-port=2049 \
protocol=tcp
add action=drop chain=tcp comment="deny NetBus" disabled=no dst-port=\
12345-12346 protocol=tcp
add action=drop chain=tcp comment="deny NetBus" disabled=no dst-port=20034 \
protocol=tcp
add action=drop chain=tcp comment="deny BackOriffice" disabled=no dst-port=\
3133 protocol=tcp
add action=drop chain=tcp comment="deny DHCP" disabled=no dst-port=67-68 \
protocol=tcp
add action=drop chain=tcp comment="Drop Blaster Worm" disabled=no dst-port=\
135-139 protocol=tcp
add action=drop chain=tcp comment="Drop Messenger Worm" disabled=no dst-port=\
135-139 protocol=udp
add action=drop chain=tcp comment="Drop Blaster Worm" disabled=no dst-port=\
445 protocol=tcp
add action=drop chain=tcp comment="Drop Blaster Worm" disabled=no dst-port=\
445 protocol=udp
add action=drop chain=tcp comment=________ disabled=no dst-port=593 protocol=\
tcp
add action=drop chain=tcp comment=________ disabled=no dst-port=1024-1030 \
protocol=tcp
add action=drop chain=tcp comment="Drop MyDoom" disabled=no dst-port=1080 \
protocol=tcp
add action=drop chain=tcp comment=________ disabled=no dst-port=1214 \
protocol=tcp
add action=drop chain=tcp comment="ndm requester" disabled=no dst-port=1363 \
protocol=tcp
add action=drop chain=tcp comment="ndm server" disabled=no dst-port=1364 \
protocol=tcp
add action=drop chain=tcp comment="screen cast" disabled=no dst-port=1368 \
protocol=tcp
add action=drop chain=tcp comment=hromgrafx disabled=no dst-port=1373 \
protocol=tcp
add action=drop chain=tcp comment=cichlid disabled=no dst-port=1377 protocol=\
tcp
add action=drop chain=tcp comment=Worm disabled=no dst-port=1433-1434 \
protocol=tcp
add action=drop chain=tcp comment="Bagle Virus" disabled=no dst-port=2745 \
protocol=tcp
add action=drop chain=tcp comment="Drop Dumaru.Y" disabled=no dst-port=2283 \
protocol=tcp
add action=drop chain=tcp comment="Drop Beagle" disabled=no dst-port=2535 \
protocol=tcp
add action=drop chain=tcp comment="Drop Beagle.C-K" disabled=no dst-port=2745 \
protocol=tcp
add action=drop chain=tcp comment="Drop MyDoom" disabled=no dst-port=\
3127-3128 protocol=tcp
add action=drop chain=tcp comment="Drop Backdoor OptixPro" disabled=no \
dst-port=3410 protocol=tcp
add action=drop chain=tcp comment=Worm disabled=no dst-port=4444 protocol=tcp
add action=drop chain=tcp comment=Worm disabled=no dst-port=4444 protocol=udp
add action=drop chain=tcp comment="Drop Sasser" disabled=no dst-port=5554 \
protocol=tcp
add action=drop chain=tcp comment="Drop Beagle.B" disabled=no dst-port=8866 \
protocol=tcp
add action=drop chain=tcp comment="Drop Dabber.A-B" disabled=no dst-port=9898 \
protocol=tcp
add action=drop chain=tcp comment="Drop Dumaru.Y" disabled=no dst-port=10000 \
protocol=tcp
add action=drop chain=tcp comment="Drop MyDoom.B" disabled=no dst-port=10080 \
protocol=tcp
add action=drop chain=tcp comment="Drop Kuang2" disabled=no dst-port=17300 \
protocol=tcp
add action=drop chain=tcp comment="Drop SubSeven" disabled=no dst-port=27374 \
protocol=tcp
add action=drop chain=tcp comment="Drop PhatBot, Agobot, Gaobot" disabled=no \
dst-port=65506 protocol=tcp
add action=drop chain=udp comment="deny TFTP" disabled=no dst-port=69 \
protocol=udp
add action=drop chain=udp comment="deny PRC portmapper" disabled=no dst-port=\
111 protocol=udp
add action=drop chain=udp comment="deny PRC portmapper" disabled=no dst-port=\
135 protocol=udp
add action=drop chain=udp comment="deny NBT" disabled=no dst-port=137-139 \
protocol=udp
add action=drop chain=udp comment="deny NFS" disabled=no dst-port=2049 \
protocol=udp
add action=drop chain=udp comment="deny BackOriffice" disabled=no dst-port=\
3133 protocol=udp
add action=accept chain=icmp comment="drop invalid connections" disabled=no \
icmp-options=0:0 protocol=icmp
add action=accept chain=icmp comment="allow established connections" \
disabled=no icmp-options=3:0 protocol=icmp
add action=accept chain=icmp comment="allow already established connections" \
disabled=no icmp-options=3:1 protocol=icmp
add action=accept chain=icmp comment="allow source quench" disabled=no \
icmp-options=4:0 protocol=icmp
add action=accept chain=icmp comment="allow echo request" disabled=no \
icmp-options=8:0 protocol=icmp
add action=accept chain=icmp comment="allow time exceed" disabled=no \
icmp-options=11:0 protocol=icmp
add action=accept chain=icmp comment="allow parameter bad" disabled=no \
icmp-options=12:0 protocol=icmp
add action=drop chain=icmp comment="deny all other types" disabled=no
/ip firewall address-list
add address=192.168.0.254 comment="ip router mikrotik" disabled=no list=router add address=10.0.0.0/8 comment="" disabled=no list=private-networks add address=172.16.0.0/12 comment="" disabled=no list=private-networks add address=192.168.0.0/16 comment="" disabled=no list=private-networks add address=192.168.1.1 comment="Modem spidi wan1" disabled=no list=exceptions add address=192.168.2.1 comment="Modem spidi wan2" disabled=no list=exceptions add address=192.168.3.1 comment="Modem spidi wan3" disabled=no list=exceptions add address=192.168.4.1 comment="Modem spidi wan4" disabled=no list=exceptions add address=192.168.5.1 comment="Modem spidi wan5" disabled=no list=exceptions add address=192.168.100.1 comment="proxy server" disabled=no list=exceptions add address=192.168.0.0/24 comment="" disabled=no list=local add address=192.168.1.1 comment="" disabled=no list=local add address=192.168.2.1 comment="" disabled=no list=local add address=192.168.3.1 comment="" disabled=no list=local add address=192.168.4.1 comment="" disabled=no list=local add address=192.168.5.1 comment="" disabled=no list=local add address=192.168.100.1 comment="" disabled=no list=local add address=192.168.0.0/24 comment="" disabled=no list=clients add address=192.168.100.1 comment="" disabled=no list=proxy add address=192.168.1.1 comment=wan1 disabled=no list=bypasswww add address=192.168.2.1 comment=wan2 disabled=no list=bypasswww add address=192.168.3.1 comment=wan3 disabled=no list=bypasswww add address=192.168.4.1 comment=wan4 disabled=no list=bypasswww add address=192.168.5.1 comment=wan5 disabled=no list=bypasswww add address=192.168.100.1 comment=proxy disabled=no list=bypasswww
/ip firewall nat
add action=redirect chain=dstnat comment="DNS REDIRECT to router" disabled=no \
dst-port=53 in-interface=lan protocol=udp src-address-list=clients \
to-ports=53
add action=redirect chain=dstnat comment="DNS REDIRECT to router" disabled=no \
dst-port=53 in-interface=lan protocol=tcp src-address-list=clients \
to-ports=53
add action=dst-nat chain=dstnat comment=proxy_external disabled=no \
dst-address-list=!bypasswww dst-port=80,3128,8080 in-interface=lan \
protocol=tcp src-address-list=clients to-addresses=192.168.100.1 \
to-ports=8080
add action=masquerade chain=srcnat comment=wan1 disabled=no out-interface=\
wan1 src-address-list=clients
add action=masquerade chain=srcnat comment=wan2 disabled=no out-interface=\
wan2 src-address-list=clients
add action=masquerade chain=srcnat comment=wan3 disabled=no out-interface=\
wan3 src-address-list=clients
add action=masquerade chain=srcnat comment=wan4 disabled=no out-interface=\
wan4 src-address-list=clients
add action=masquerade chain=srcnat comment=wan5 disabled=no out-interface=\
wan5 src-address-list=clients
add action=masquerade chain=srcnat comment=wan1 disabled=no out-interface=\
wan1 src-address-list=proxy
add action=masquerade chain=srcnat comment=wan2 disabled=no out-interface=\
wan2 src-address-list=proxy
add action=masquerade chain=srcnat comment=wan3 disabled=no out-interface=\
wan3 src-address-list=proxy
add action=masquerade chain=srcnat comment=wan4 disabled=no out-interface=\
wan4 src-address-list=proxy
add action=masquerade chain=srcnat comment=wan5 disabled=no out-interface=\
wan5 src-address-list=proxy
/ip firewall mangle
add action=mark-packet chain=prerouting comment=\
"MARK PACKET DIRECT to proxy clients-up" disabled=no dst-address-list=\
proxy dst-port=3128,8080 in-interface=lan new-packet-mark=clients-up \
passthrough=no protocol=tcp
add action=mark-packet chain=prerouting comment="MARK PACKET LOCAL local-up" \
disabled=no dst-address-list=local in-interface=lan new-packet-mark=\
clients-local-up passthrough=no src-address-list=clients
add action=mark-packet chain=prerouting comment=\
"MARK PACKET clients tcp port 80,3128,8080 REDIRECT to proxy" disabled=no \
dst-address-list=!bypasswww dst-port=80,3128,8080 in-interface=lan \
new-packet-mark=clients-up-www passthrough=no protocol=tcp \
src-address-list=clients
add action=mark-packet chain=prerouting comment=\
"MARK PACKET clients-up" disabled=no in-interface=lan \
new-packet-mark=clients-up passthrough=yes src-address-list=clients
add action=mark-packet chain=forward comment="MARK Proxy Cache Hits" \
disabled=no dscp=12 new-packet-mark=proxy-hit passthrough=no protocol=tcp \
src-port=8080
add action=mark-packet chain=forward comment=\
"MARK PACKET clients-down from proxy" disabled=no dst-address-list=\
clients new-packet-mark=clients-down passthrough=no protocol=tcp \
src-address-list=proxy src-port=8080
add action=mark-packet chain=forward comment="MARK PACKET LOCAL clients-down" \
disabled=no dst-address-list=clients new-packet-mark=clients-local-down \
passthrough=no src-address-list=local
add action=mark-packet chain=forward comment=\
"MARK PACKET clients-down" disabled=no dst-address-list=clients \
new-packet-mark=clients-down passthrough=no
add action=mark-connection chain=prerouting comment=LB_PCC connection-state=\
new disabled=no dst-address-list=!local dst-address-type=!local \
in-interface=lan new-connection-mark=wan5-con passthrough=yes \
per-connection-classifier=both-addresses:5/0 src-address-list=clients
add action=mark-routing chain=prerouting comment=LB_PCC connection-mark=\
wan5-con disabled=no in-interface=lan new-routing-mark=wan5 passthrough=no
add action=mark-connection chain=prerouting comment=LB_NTH connection-state=\
new disabled=no dst-address-list=!local in-interface=proxy \
new-connection-mark=wan5-con nth=5,1 passthrough=yes
add action=mark-routing chain=prerouting comment=LB_NTH connection-mark=\
wan5-con disabled=no in-interface=proxy new-routing-mark=wan5 \
passthrough=no
add action=mark-connection chain=prerouting comment=LB_PCC connection-state=\
new disabled=no dst-address-list=!local dst-address-type=!local \
in-interface=lan new-connection-mark=wan4-con passthrough=yes \
per-connection-classifier=both-addresses:4/0 src-address-list=clients
add action=mark-routing chain=prerouting comment=LB_PCC connection-mark=\
wan4-con disabled=no in-interface=lan new-routing-mark=wan4 passthrough=no
add action=mark-connection chain=prerouting comment=LB_NTH connection-state=\
new disabled=no dst-address-list=!local in-interface=proxy \
new-connection-mark=wan4-con nth=4,1 passthrough=yes
add action=mark-routing chain=prerouting comment=LB_NTH connection-mark=\
wan4-con disabled=no in-interface=proxy new-routing-mark=wan4 \
passthrough=no
add action=mark-connection chain=prerouting comment=LB_PCC connection-state=\
new disabled=no dst-address-list=!local dst-address-type=!local \
in-interface=lan new-connection-mark=wan3-con passthrough=yes \
per-connection-classifier=both-addresses:3/0 src-address-list=clients
add action=mark-routing chain=prerouting comment=LB_PCC connection-mark=\
wan3-con disabled=no in-interface=lan new-routing-mark=wan3 passthrough=\
no
add action=mark-connection chain=prerouting comment=LB_NTH connection-state=\
new disabled=no dst-address-list=!local in-interface=proxy \
new-connection-mark=wan3-con nth=3,1 passthrough=yes
add action=mark-routing chain=prerouting comment=LB_NTH connection-mark=\
wan3-con disabled=no in-interface=proxy new-routing-mark=wan3 \
passthrough=no
add action=mark-connection chain=prerouting comment=LB_PCC connection-state=\
new disabled=no dst-address-list=!local dst-address-type=!local \
in-interface=lan new-connection-mark=wan2-con passthrough=yes \
per-connection-classifier=both-addresses:2/0 src-address-list=clients
add action=mark-routing chain=prerouting comment=LB_PCC connection-mark=\
wan2-con disabled=no in-interface=lan new-routing-mark=wan2 passthrough=\
no
add action=mark-connection chain=prerouting comment=LB_NTH connection-state=\
new disabled=no dst-address-list=!local in-interface=proxy \
new-connection-mark=wan2-con nth=2,1 passthrough=yes
add action=mark-routing chain=prerouting comment=LB_NTH connection-mark=\
wan2-con disabled=no in-interface=proxy new-routing-mark=wan2 \
passthrough=no
add action=mark-connection chain=prerouting comment=LB_PCC connection-state=\
new disabled=no dst-address-list=!local dst-address-type=!local \
in-interface=lan new-connection-mark=wan1-con passthrough=yes \
per-connection-classifier=both-addresses:1/0 src-address-list=clients
add action=mark-routing chain=prerouting comment=LB_PCC connection-mark=\
wan1-con disabled=no in-interface=lan new-routing-mark=wan1 passthrough=\
no
add action=mark-connection chain=prerouting comment=LB_NTH connection-state=\
new disabled=no dst-address-list=!local in-interface=proxy \
new-connection-mark=wan1-con nth=1,1 passthrough=yes
add action=mark-routing chain=prerouting comment=LB_NTH connection-mark=\
wan1-con disabled=no in-interface=proxy new-routing-mark=wan1 \
passthrough=no
Baris-baris rule mangle yang berwarna hijau itu ditulis secara otomatis melalui script yang akan dijelaskan nanti.
param
Saat router reboot script param di bawah ini akan dieksekusi:
# # script: param # # Jumlah koneksi wan :global nwan 5; # daftar ip internet yang dirouting secara statik :global ips "202.134.1.10,202.155.0.20,125.160.0.97,202.154.1.2,202.155.0.15"; # daftar ip wan atau gateway :global gws "192.168.1.1,192.168.2.1,192.168.3.1,192.168.4.1,192.168.5.1"; # nilai atau score untuk masing-masing wan :global scrs "2,4,8,16,32"; :global SCORE 0;
Variable score scrs untuk menyimpan nilai atau score per wan sedangkan SCORE untuk menyimpan status online semua wan:
- Nilai SCORE 0 berarti semua WAN tidak online.
- Jika WAN 1 online maka nilai SCORE menjadi bertambah 2.
- Jika WAN 2 online maka nilai SCORE menjadi bertambah 4.
- Jika WAN 3 online maka nilai SCORE menjadi bertambah 8.
- Jika WAN 4 online maka nilai SCORE menjadi bertambah 16.
- Jika WAN 5 online maka nilai SCORE menjadi bertambah 32.
- Jika semua WAN online nilai SCORE adalah 2+4+8+16+32 = 62.
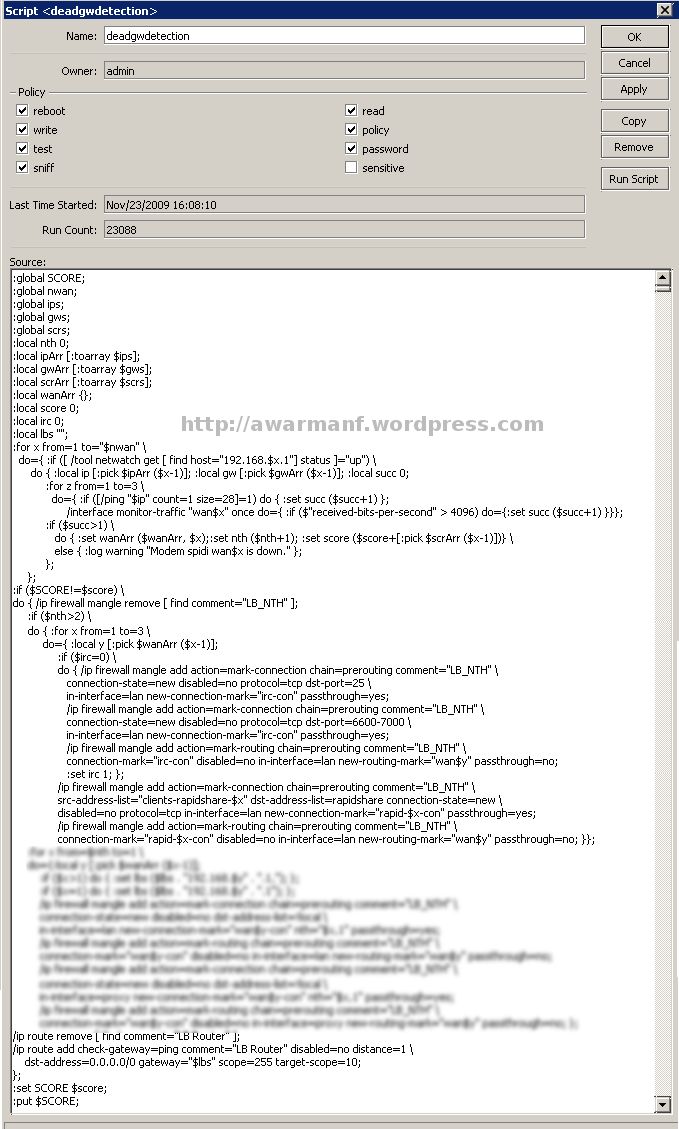
deadgwdetection
Script ini dijalankan via schedule setiap 120 detik atau 2 menit
#
# script: deadgwdetection
#
:global SCORE;
:global nwan;
:global ips;
:global gws;
:global scrs;
:local nth 0;
:local ipArr [:toarray $ips];
:local gwArr [:toarray $gws];
:local scrArr [:toarray $scrs];
:local wanArr {};
:local score 0;
:local lbs "";
:for x from=1 to="$nwan" \
do={ :if ([ /interface ethernet get "wan$x" running ]) \
do { :local ip [:pick $ipArr ($x-1)]; :local gw [:pick $gwArr ($x-1)]; :local succ 0;
:for z from=1 to=3 \
do={ :if ([/ping "$ip" count=1 size=28]=1) do { :set succ ($succ+1) };
/interface monitor-traffic "wan$x" once do={ :if ($"rx-bits-per-second" > 4096) do={:set succ ($succ+1) }}};
:if ($succ>1) \
do { :set wanArr ($wanArr, $x);:set nth ($nth+1); :set score ($score+[:pick $scrArr ($x-1)])} \
else { :log warning "Modem spidi wan$x is down." };
};
};
:local ptr [ /system logging find topics="info"];
/system logging disable $ptr;
:if ($SCORE!=$score) \
do { /ip firewall mangle remove [ find comment="LB_NTH" ];
/ip firewall mangle remove [ find comment="LB_PCC" ];
:for x from=$nth to=1 \
do={:local y [:pick $wanArr ($x-1)];
:if ($x>1) do { :set lbs ($lbs . "192.168.$y" . ".1,"); };
:if ($x=1) do { :set lbs ($lbs . "192.168.$y" . ".1"); };
/ip firewall mangle add action=mark-connection chain=prerouting comment="LB_PCC" \
connection-state=new disabled=no dst-address-list=!local dst-address-type=!local \
in-interface=lan src-address-list=clients new-connection-mark="wan$y-con" \
per-connection-classifier="both-addresses:$x/0" passthrough=yes;
/ip firewall mangle add action=mark-routing chain=prerouting comment="LB_PCC" \
connection-mark="wan$y-con" disabled=no in-interface=lan new-routing-mark="wan$y" passthrough=no;
/ip firewall mangle add action=mark-connection chain=prerouting comment="LB_NTH" \
connection-state=new disabled=no dst-address-list=!local \
in-interface=proxy new-connection-mark="wan$y-con" nth="$x,1" passthrough=yes;
/ip firewall mangle add action=mark-routing chain=prerouting comment="LB_NTH" \
connection-mark="wan$y-con" disabled=no in-interface=proxy new-routing-mark="wan$y" passthrough=no; };
/ip route remove [ find comment="LB Router" ];
/ip route add check-gateway=ping comment="LB Router" disabled=no distance=1 \
dst-address=0.0.0.0/0 gateway="$lbs" scope=255 target-scope=10;
};
/system logging enable $ptr;
:set SCORE $score;
:put $SCORE;
Penjelasan:
- Pertama deteksi apakah koneksi fisik ke wan running atau tidak (baris 17).
- Kedua apakah melalui wan tersebut bisa ping ke tertentu (baris 20).
- Jika tidak bisa diping cek trafik received yang melalui wan tadi apakah melewati threshold atau ambang batas tertentu sehingga bisa dianggap wan ini online (baris 21).
- Jika salah satu di atas berhasil, no 2 atau 3, maka naikkan jumlah wan dan tulis link wan yang aktif (baris 23). Jika semua gagal tulis di log bahwa koneksi melalui wan ini down (baris 24).
- Agar tidak terlalu banyak output ke log, matikan untuk sementara fungsi ini di baris 28.
- Jika ada perubahan jumlah koneksi atau nilai SCORE (baris 29) maka buat baru baris-baris mangle (baris 30-31).
- Baris 34-46 menulis ip firewall mangle Load Balancing PCC untuk koneksi non browsing (tcp port 80) dari clients dan Load Balancing NTH untuk koneksi dari proxy.
- Baris 48-50 menulis routing default yang baru untuk mikrotik.
- Fungsi logging diaktifkan kembali di baris 52.
- Nilai SCORE dari jumlah koneksi sekarang disimpan (baris 53-54).
Sekarang aktifkan schedule untuk dua script di atas:
/system scheduler
add comment="" disabled=no interval=0s name=sch-param-startup on-event=param \
policy=read,write,test start-time=startup
add comment="" disabled=no interval=2m name=sch-deadgwdetction on-event=\
deadgwdetection policy=read,write,test start-date=jan/01/1970 \
start-time=00:00:10





 untuk menyempurnakan Aksi Tipu Tipu tadi.. wajib kita tambahkan settingan ini..
untuk menyempurnakan Aksi Tipu Tipu tadi.. wajib kita tambahkan settingan ini.. heheh
heheh 
